How Can I Secure My Earnings From My Cryptocurrency Mining Rig?
In this article, you will learn some essential tips on how to protect and secure your earnings from your cryptocurrency mining rig. We will explore various strategies, such as using secure wallets, implementing two-factor authentication, and regularly updating your software. By following these measures, you can ensure the safety of your hard-earned cryptocurrencies and minimize the risk of any potential security breaches. So, let’s dive in and discover how you can safeguard your earnings from your mining rig!
Introduction
Introduction to cryptocurrency mining rig and earnings
Cryptocurrency mining has become a popular way for individuals to earn money in the digital world. By utilizing powerful computer hardware, known as a mining rig, individuals can solve complex mathematical problems and receive cryptocurrency as a reward. However, as with any type of online activity involving valuable assets, it is important to take steps to secure your earnings and protect yourself from potential threats.
Choosing a secure mining rig
Factors to consider when selecting a secure mining rig
Before diving into the world of cryptocurrency mining, it is crucial to choose a mining rig that provides a high level of security. Factors to consider include the rig’s processing power, energy efficiency, and cooling capabilities. Additionally, you should take into account the reputation of the manufacturer and the availability of customer support.
Researching and comparing mining rig options
To ensure you choose the most secure mining rig for your needs, it is important to conduct thorough research and compare different options. Look for reviews and user experiences to gain insights into the reliability and security of different models. Consider joining online forums or communities dedicated to mining to get advice from experienced miners who can provide valuable recommendations.
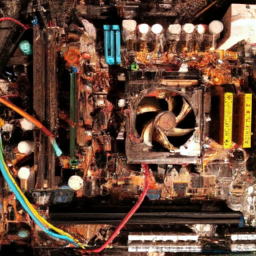
Securing the mining rig hardware
Physical security measures for the mining rig
The physical security of your mining rig is essential to protect it from theft or damage. You should store the rig in a secure location, such as a locked room or a dedicated mining farm. Install surveillance cameras or an alarm system to deter potential thieves. It may also be beneficial to use hardware enclosures or locks to prevent unauthorized access to the rig.
Protecting against theft or damage
Aside from physical security measures, it is important to protect your mining rig from theft or damage by insuring it. Check with your insurance provider to see if they offer coverage for mining equipment. Additionally, consider investing in a backup power supply to protect your rig from unexpected power outages. Regularly check the rig for any signs of wear or damage and perform necessary maintenance to ensure its longevity.
Securing the mining rig software
Using trusted mining software and operating systems
The software that runs your mining rig plays a crucial role in its security. It is important to use trusted mining software and operating systems that have been tested and verified by reputable sources. Avoid downloading software from unknown or unreliable websites, as it may contain malware or other security vulnerabilities. Stick to well-known mining software providers and regularly update the software to patch any vulnerabilities.
Implementing firewalls and antivirus software
To further enhance the security of your mining rig, it is important to implement firewalls and antivirus software. Firewalls act as a barrier between your mining rig and the outside world, filtering incoming and outgoing network traffic. Antivirus software provides an additional layer of protection by detecting and removing any malware or viruses that may infect your rig. Regularly update both the firewall and antivirus software to ensure they can effectively combat new threats.
Setting up a secure mining pool
Choosing a reliable and secure mining pool
mining pools are groups of miners who work together to increase their chances of solving mathematical problems and earning cryptocurrency rewards. When choosing a mining pool, it is crucial to select one that has a strong reputation for being reliable and secure. Look for pools with a large number of active miners and a proven track record of consistent payouts. Avoid pools that have experienced frequent downtimes or security breaches.
Configuring pool security settings
Once you have chosen a mining pool, take the time to configure the security settings provided by the pool. Enable features such as two-factor authentication, which adds an extra layer of security by requiring a second form of verification, such as a unique code sent to your mobile device. Additionally, consider monitoring the pool’s security measures on a regular basis to ensure your earnings are well-protected.
Implementing wallet security
Selecting a secure cryptocurrency wallet
A cryptocurrency wallet is a digital storage solution for your earned cryptocurrency. It is important to choose a secure wallet that offers strong encryption and multi-factor authentication options. Look for wallets that have a good reputation and have been audited by cybersecurity professionals. Avoid online wallets or exchanges, as they are more vulnerable to hacking attempts.
Enabling two-factor authentication and strong passwords
Once you have selected a cryptocurrency wallet, make sure to enable two-factor authentication (2FA) to further secure your earnings. 2FA adds an extra layer of security by requiring a second form of verification, such as a unique code or fingerprint scan. Additionally, use strong, unique passwords for your wallet and regularly update them to minimize the risk of unauthorized access.
Regularly monitoring earnings
Using mining software to track earnings
To ensure the security of your earnings, it is important to regularly monitor your mining rig’s performance and track your earnings. Utilize mining software that provides detailed statistics on your mining activity, such as hash rate and estimated earnings. Regularly review these statistics and compare them to your expected earnings to identify any potential issues or irregularities.
Identifying suspicious activity or irregularities
During the process of monitoring your earnings, it is important to stay vigilant for any signs of suspicious activity or irregularities. Monitor your mining pool’s payout history and ensure that your earnings are being deposited as expected. Be wary of any sudden changes in your earnings or unexplained fluctuations in mining performance, as these could be indicators of a security breach or other issues.
Backup and disaster recovery
Creating regular backups of earnings and wallet data
Similar to any important digital assets, it is crucial to create regular backups of your earnings and wallet data. This involves making copies of your wallet’s private keys or recovery phrases and storing them in a secure offline location, such as a safe or a hardware wallet. Regularly update these backups to ensure they reflect the most recent state of your earnings and wallet.
Developing a disaster recovery plan
In addition to backups, it is important to develop a disaster recovery plan in case of unforeseen events, such as hardware failure or theft. This plan should outline the steps you will take to recover your earnings, including contacting support teams, reconfiguring your mining rig, and restoring your wallet from backups. Having a well-defined plan in place will help minimize any potential financial losses and ensure you can quickly resume your mining activities.
Protecting against scams and frauds
Educating yourself about common scams in the cryptocurrency industry
The cryptocurrency industry is not immune to scams and frauds. It is important to educate yourself about common scams and stay informed about the latest developments in the industry. Keep up to date with news and reputable online sources to identify potential threats and protect yourself from falling victim to fraudulent schemes.
Avoiding phishing attacks and fraudulent investment schemes
Phishing attacks are a common method used by scammers to steal sensitive information, such as login credentials or wallet details. Be cautious of suspicious emails or messages that request personal information or instruct you to download files or visit unknown websites. Additionally, be wary of any investment schemes that promise high returns with little to no risk. Remember, if something sounds too good to be true, it probably is.
Conclusion
Summary of key strategies for securing earnings from a cryptocurrency mining rig
In conclusion, securing your earnings from a cryptocurrency mining rig requires a multi-faceted approach that covers both hardware and software security measures. By choosing a secure mining rig, implementing physical and software security measures, using a reliable mining pool, and protecting your wallet with strong authentication, you can significantly reduce the risk of theft or loss. Regularly monitoring your earnings, implementing backup and disaster recovery measures, and staying vigilant against scams and frauds are also crucial in maintaining the security of your earnings. By following these strategies, you can enjoy the benefits of cryptocurrency mining while ensuring the safety of your hard-earned earnings.